Ermit Secure IoT Module handles connectivity security as a dedicated hardware layer so your host device stays simple, your cloud stays yours, and your team stays focused on the product. Device identity and cryptographic secrets are protected by a dedicated hardware secure element, never exposed in software. The module works with your existing cloud infrastructure, manages certificates autonomously, and ensures firmware and data are never lost in the field without locking you into a proprietary platform.
Building the product is the hard part. Securing its connectivity shouldn't be.
IoT security is a discipline of its own, not something your product team should have to build from scratch.
Ermit Secure IoT Module handles connectivity security as a dedicated hardware layer so your host device stays simple, your cloud stays yours, and your team stays focused on the product. Device identity and cryptographic secrets are protected by a dedicated hardware secure element, never exposed in software. The module works with your existing cloud infrastructure, manages certificates autonomously, and ensures firmware and data are never lost in the field without locking you into a proprietary platform.
Shipping a connected product is the beginning of a security responsibility.
Most companies that build connected products are not IoT companies. They know their domain, industrial equipment, medical devices, consumer appliances, but secure connectivity, certificate management, and cybersecurity compliance are a different discipline entirely.
The result is predictable: shared keys across devices, certificates that expire unnoticed, no update mechanism in the field, a host device directly exposed to the internet. The answer isn't to turn every product team into a security team.
operational benefits
Your team stays focused on the product.
Security, certificate lifecycle, and hardware identity are handled by the module, without requiring your engineering team to develop or maintain IoT security expertise.
One interface. Everything else is transparent.
The only integration point is the communication interface between host and module. Security, connectivity, and credential management happen transparently, invisible to your host firmware.
Compliance is built in and demonstrable.
CRA, RED, and ETSI EN 303 645 alignment is not an architectural afterthought, it is embedded in the design. The documentation trail is already there.
Built for the field, not just for integration.
The module stays updated, certificates don't expire silently, and data is never lost offline. Your product remains secure for its entire lifecycle - not just at shipping.
Your cloud stays yours.
The module works with your existing cloud infrastructure. No proprietary platform required, no vendor lock-in.
How it fits into your product.
Three surfaces. One secure lifecycle.
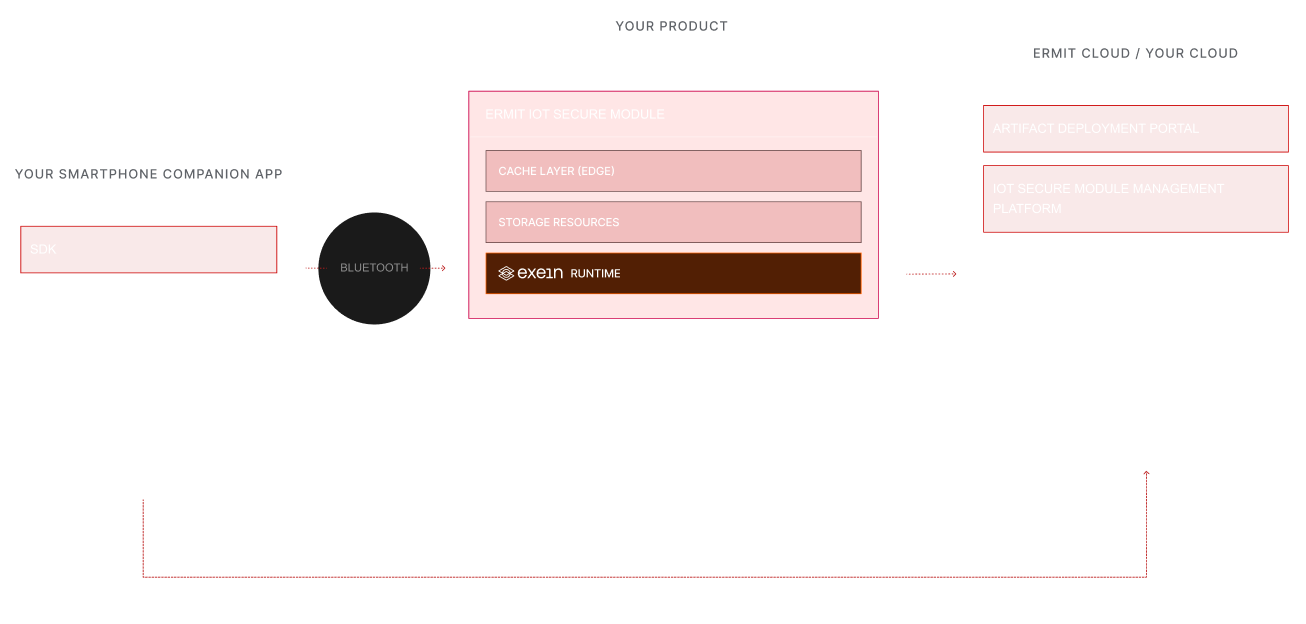
ONE INTEGRATION. END-TO-END
We secure the product at the edge, then give teams the tools to deploy, update, and prove compliance at scale.
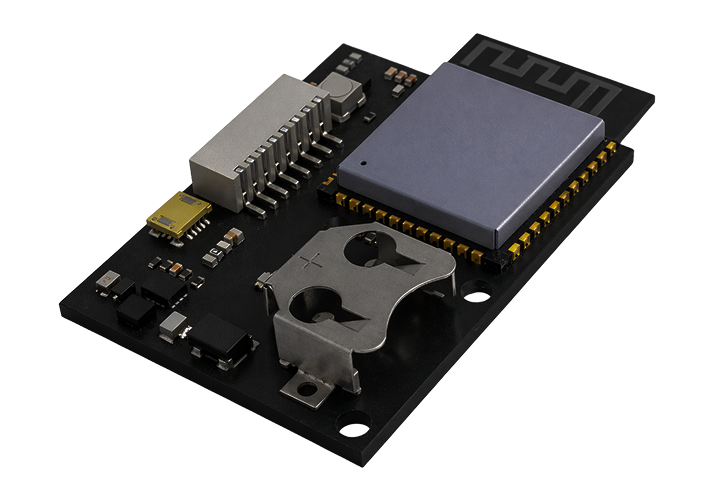
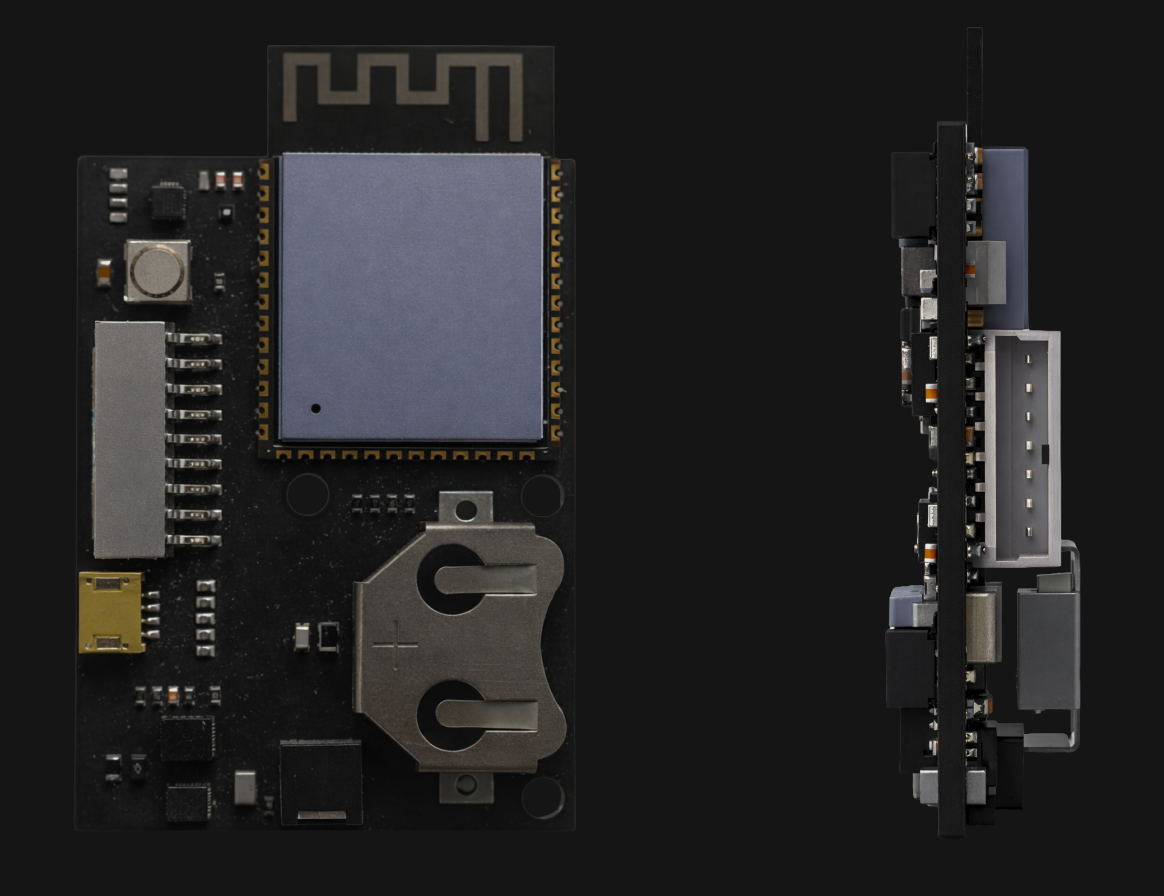
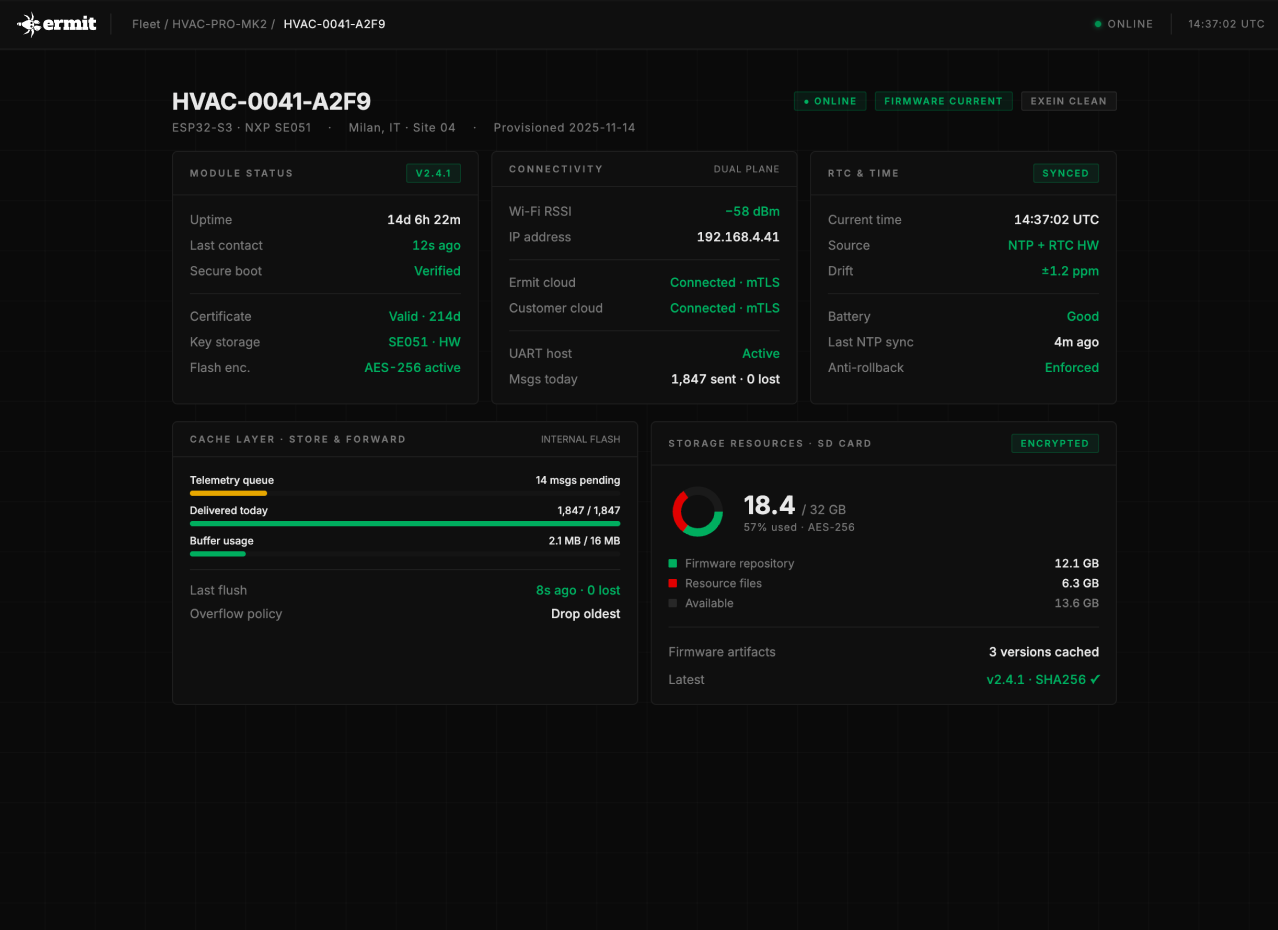
The Module
A compact security + connectivity kernel built for the field with hardware-backed identity, autonomous certificates, and local resilience.
-
The module also exposes expansion connectors, allowing additional field buses and interfaces - Ethernet, LTE, Modbus, CAN, RS-485 - to be added as plug-in boards without redesigning the base hardware.
Delivery Suite
The module is one part of a complete delivery system. Everything around it is designed to make deployment, updates, and field operations manageable at scale, without building the infrastructure yourself.
-
Integrated Exein Runtime runs directly on the module, providing continuous behavioral monitoring, anomaly detection, and incident reporting - adding an active security layer on top of the architectural protections.
Your questions. Straight answers.
-
The module is compact and designed for straightforward mechanical and electrical integration - available with both board-to-board and field-wired interfaces. If your board already exposes a 3.3V–12V power rail and a TTL serial line, no PCB redesign is required. It carries CE and RoHS certification, reducing your compliance workload. Technical documentation and a reference design are available to accelerate integration.
-
The module supports Microsoft Azure IoT Hub and Amazon AWS IoT Core natively, communicating through the standard protocols defined by each platform - no proprietary protocol, no middleware layer required between the module and your existing backend.
-
It depends on the complexity of your product's communication architecture, but most integrations are completed within a few weeks. The reference design and technical documentation are structured to reduce the time from evaluation to first working prototype. An AI assistant is also available to support the implementation of the communication protocol.
-
Ermit handles module firmware updates and security patches autonomously through a dedicated management channel, completely separate from your application data. If you prefer full control, the entire management infrastructure can be transferred to and operated within your own environment.
-
The module operates on top of your cloud infrastructure - Azure IoT Hub or AWS IoT Core - which you own and control independently.
Compliance, backed by evidence
Reduce your compliance surface and documentation effort - with an architecture built to meet requirements by design.
Proof Matrix
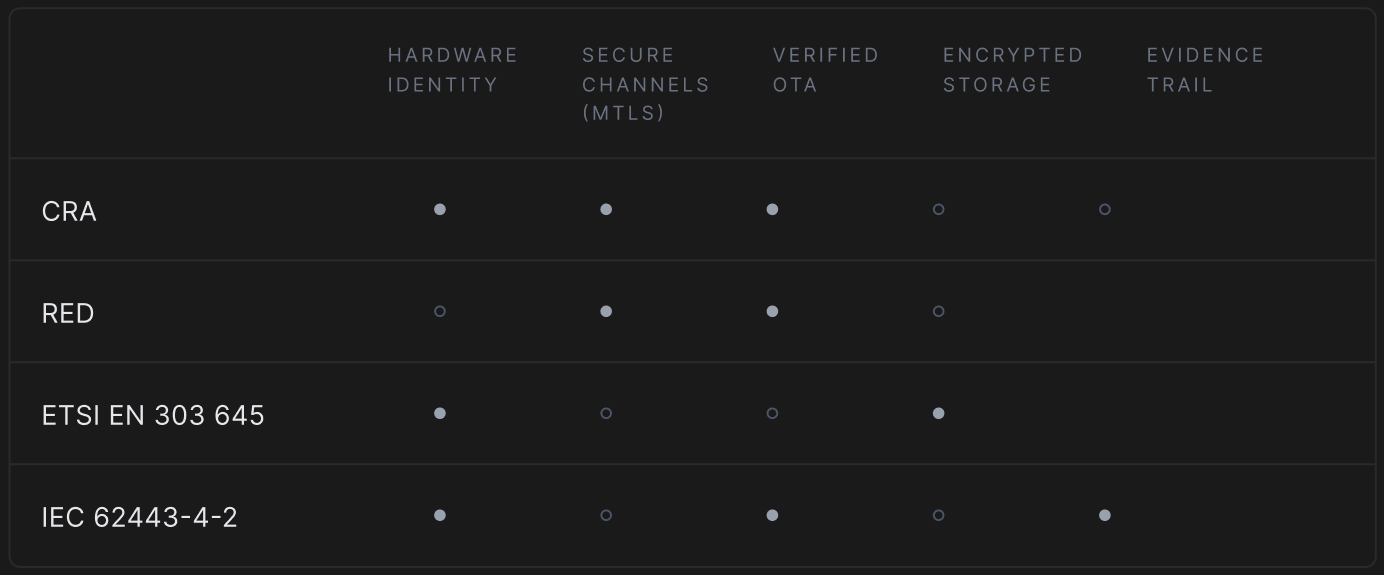
Coverage is architectural - designed for assessment support, not retrofitted after the fact.
CYBER RESILIENCE ACT
Application Dates
2026 September 11th
Application of Article 14
Notification of Vulnerabilities & incidents. Applicable on product placed on the market before December 11th 2027.
2027 December 11th
Full Application of CRA
Applicable on new product placed on the market from December 11th 2027, or Product with substantial modification & placed on the market before.
2028 June 11th
End of Transition Period
Product cyber certified (EU type) before CRA must be re-certified (ex. CE RED)*
Source: Article 69 CRA
*except if any regulation voted or expiration before this deadline



